Our Technology
Software-based security for contested and mission-critical environments
The Zero Trust X technology suite addresses 5G security through three complementary approaches: device-centric threat detection for identifying basestation-level attacks, quantum-proof communications shielding deployed on commercial devices, and zero-trust security enforcement for cloud-native 5G core networks.
Communications Shielding
Communication security that remains unbreakable even against future quantum computing threats, running directly on standard 5G devices already available on the market.
Key Features
- Denial-of-service (DoS) attack protection
- Jamming attack protection
- Man-in-the-middle (MITM) attack protection
- Quantum-proof data confidentiality
- Deployed on standard 5G COTS UE devices
Performance
- Provable data availability guaranteed
- Provable data confidentiality guaranteed
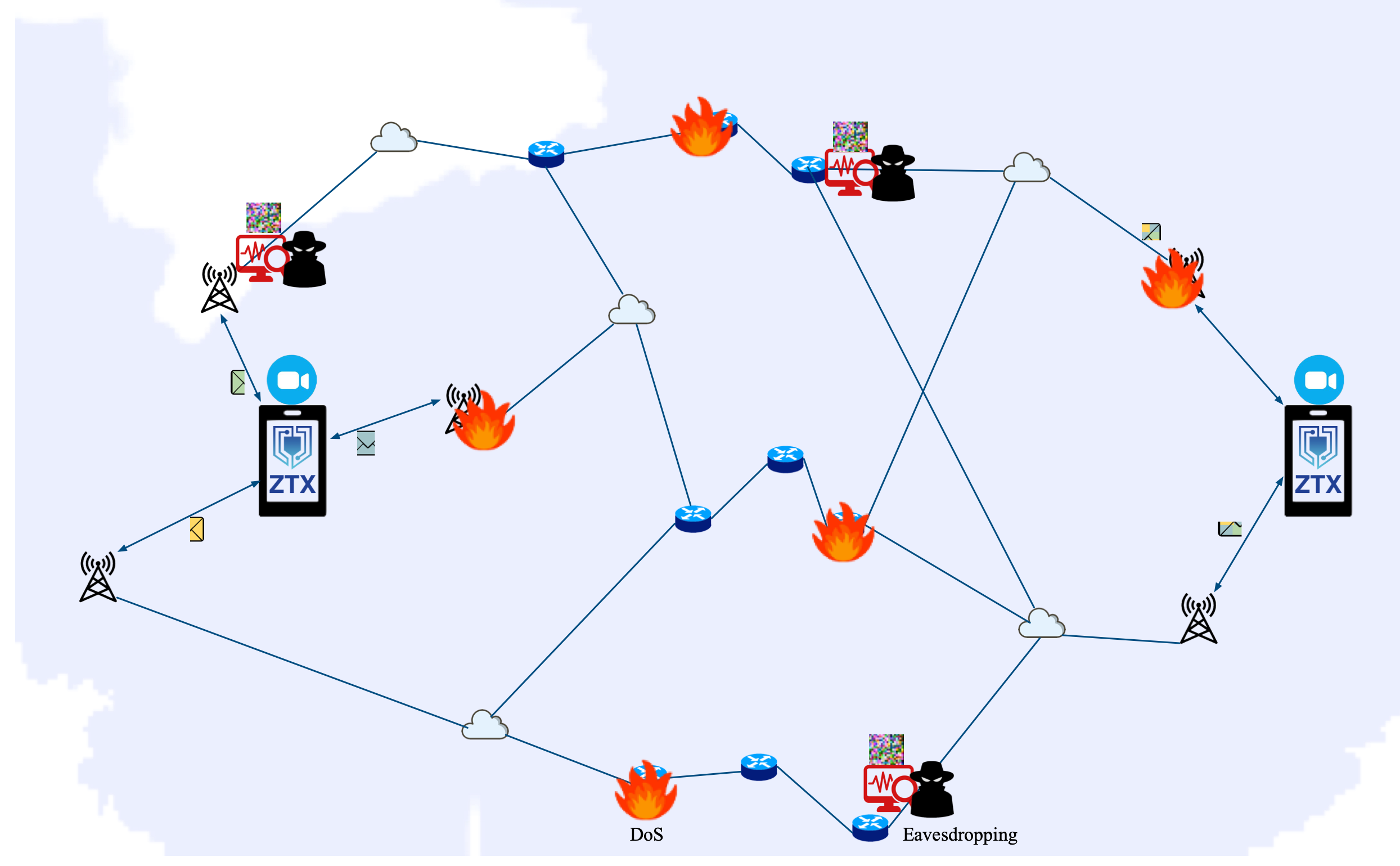
Communications shielding: eavesdropper sees only garbled data, while intended receivers maintain uninterrupted access to clear communications
Threat Detection
A 5G device-centric threat detection system that identifies abnormalities from 5G Standalone (SA) and Non-Standalone (NSA) basestations.
- Detects known signature-based attacks
- Detects unknown and zero-day attacks through anomaly analysis
- Device-centric approach requiring no infrastructure-side deployment
Deployed and verified against controlled malicious 5G base stations in lab environments.
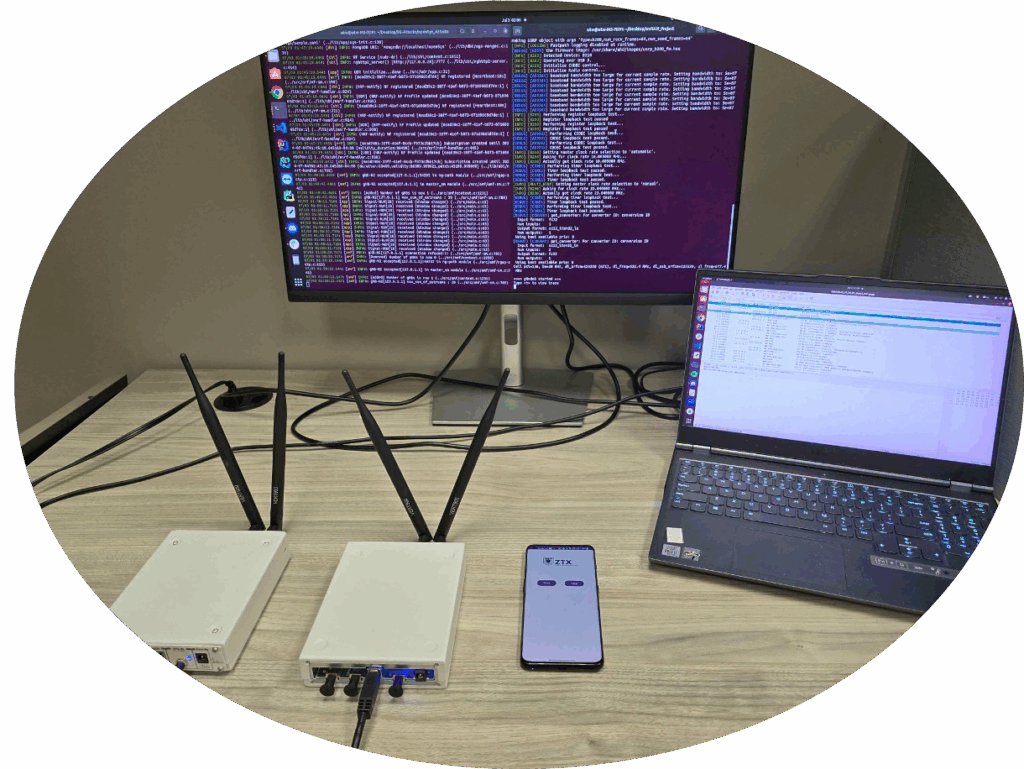
Threat detection testbed with controlled 5G base stations
5G Core Security
Zero Trust X Security Enforcement Microservice (ZTX-SEM) is a protocol-agnostic zero-trust security solution designed for cloud-native 5G control plane deployments. It secures complex network functions deployed as microservices in Kubernetes environments.
Key Features
- Protocol-agnostic security across all communication protocols
- Lightweight packet interception mechanism
- Proactive authentication strategy that reduces latency and ensures continuous readiness
- Optimized secret key lookup for accelerated encrypted communication
Performance
Tested on a Kubernetes-deployed 5G control plane (core), ZTX-SEM outperforms existing solutions such as Istio:
- 75% reduction in resource utilization
- 28% reduction in session setup times
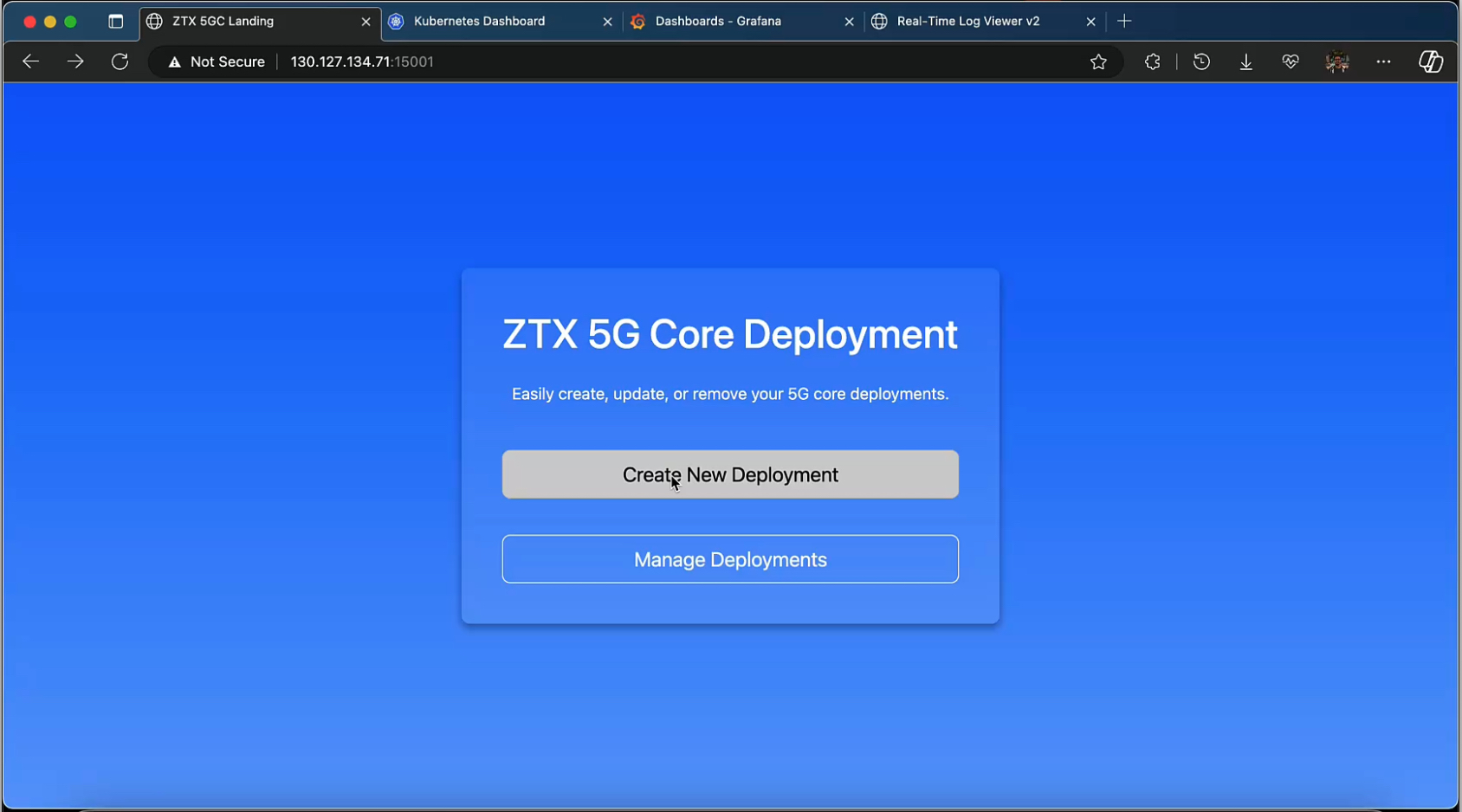
ZTX 5G Core deployment management interface
Potential Applications
Defense & Government
5G security for defense, government, and security-focused organizations operating over commercial or allied 5G infrastructure.
Critical Infrastructure
Security for essential services and industries adopting 5G connectivity.
Cloud-Native 5G Deployments
Zero-trust security enforcement for operators and enterprises deploying cloud-native 5G core networks.
Research & Development
Partner with us on emerging 5G/6G security challenges.
- Research programs and partnerships
- Technology evaluation and integration
- Custom solution development
Discuss Your Requirements
Contact us for technical discussions and capability demonstrations.
Contact Us